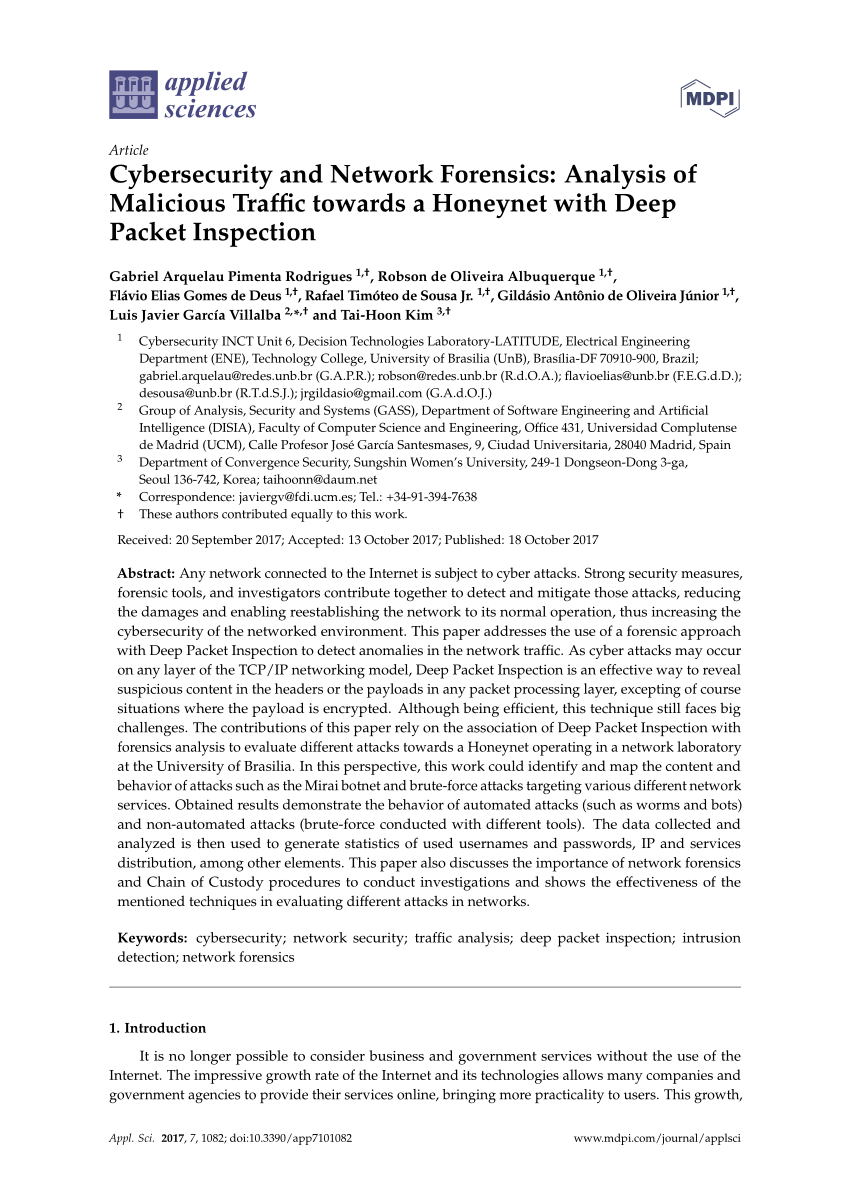
PDF) Cybersecurity and Network Forensics: Analysis of Malicious Traffic towards a Honeynet with Deep Packet Inspection
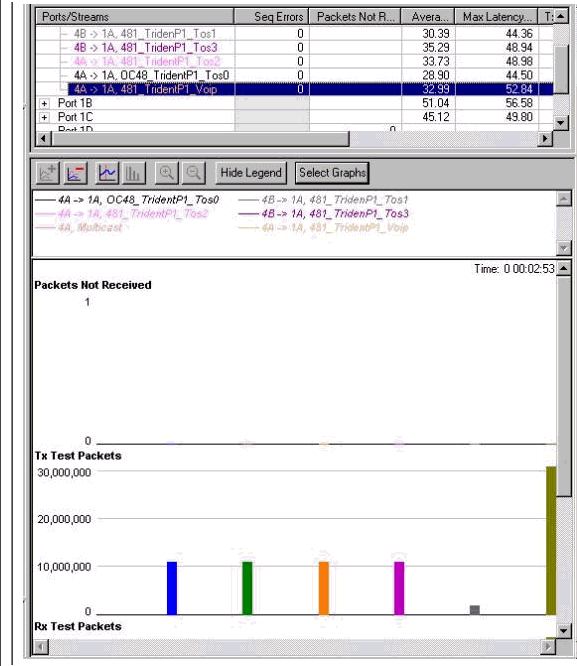
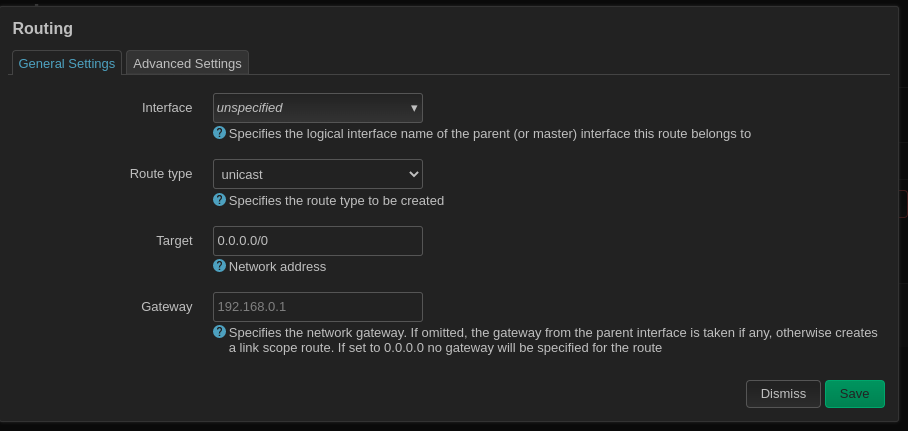
WRED and MDRR on the Cisco 12000 Series Internet Router with a Mix of Unicast, Multicast, and Voice Traffic Configuration Example - Cisco
Applied Sciences | Free Full-Text | Cybersecurity and Network Forensics: Analysis of Malicious Traffic towards a Honeynet with Deep Packet Inspection
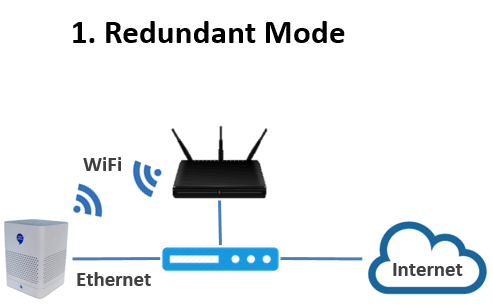
![Basic Small Branch Network System Assurance Guide - System Implementation [Design Zone for Branch/WAN] - Cisco Basic Small Branch Network System Assurance Guide - System Implementation [Design Zone for Branch/WAN] - Cisco](https://www.cisco.com/c/dam/en/us/td/i/300001-400000/300001-310000/302001-303000/302960.tif/_jcr_content/renditions/302960.jpg)